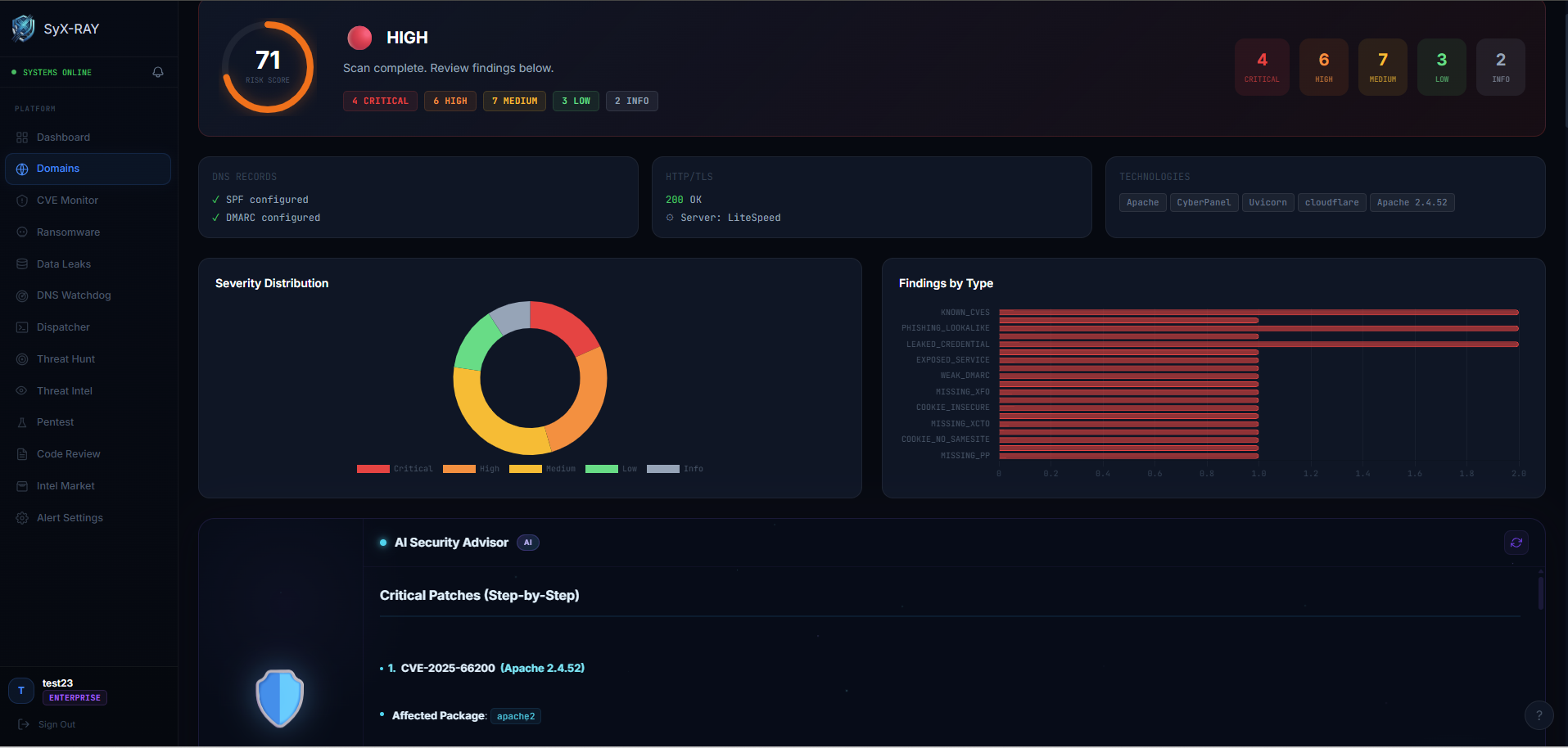
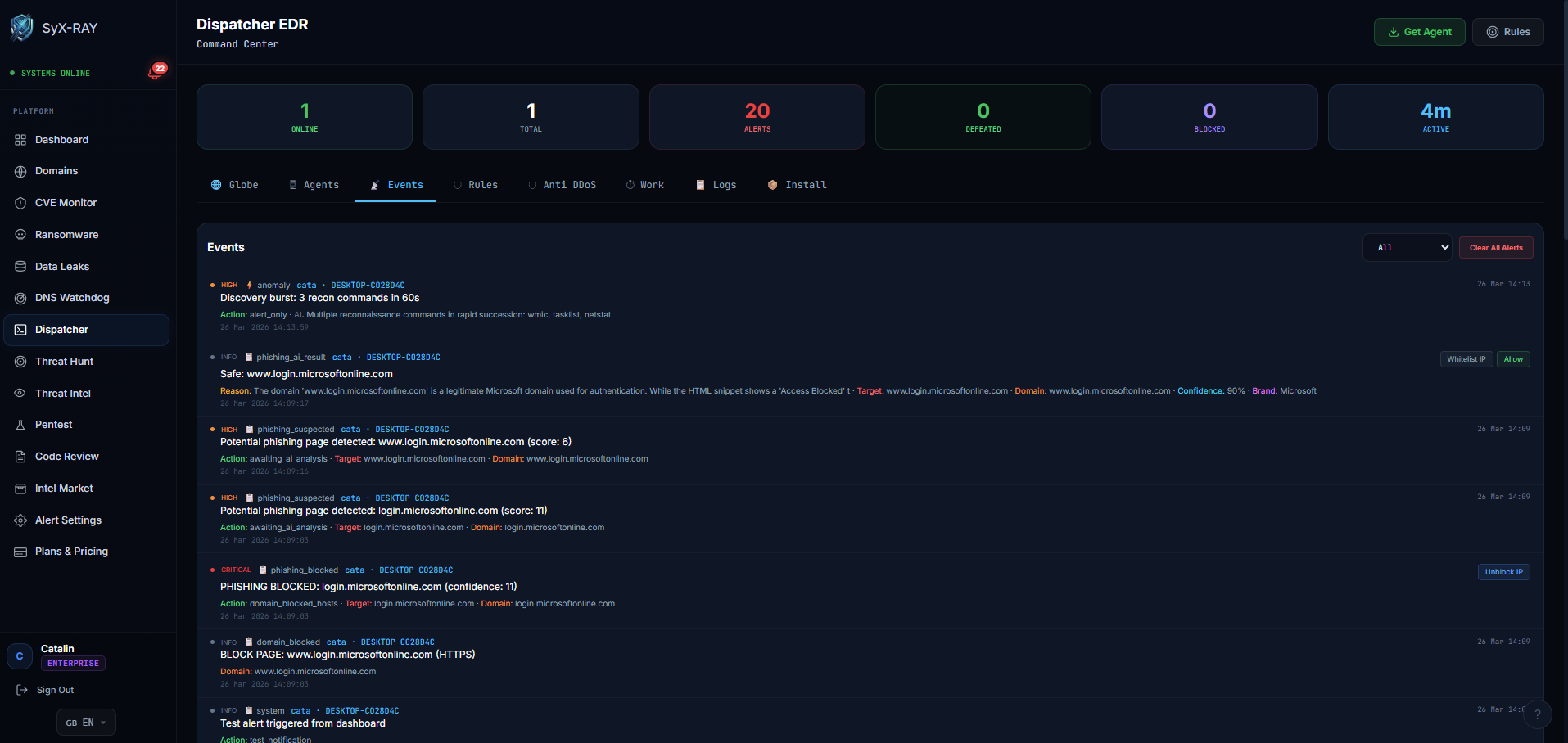
The SyX-RAY Dispatcher deploys a lightweight agent on your endpoints (Windows, Linux, macOS). It monitors processes, network connections, and file changes in real time. When threats are detected — malware, C2 beaconing, lateral movement — the agent acts instantly: killing processes, quarantining files, and blocking hostile IPs. All events are classified via MITRE ATT&CK and reported to your dashboard. The AI detection engine runs entirely inside a sandboxed environment, analyzing only behavioral data (process actions, system calls, network patterns) — never interpreting raw payload content. This means attackers cannot poison the LLM through crafted payloads, as the sandbox is fully isolated from the platform and the AI model never receives untrusted input as instructions.